

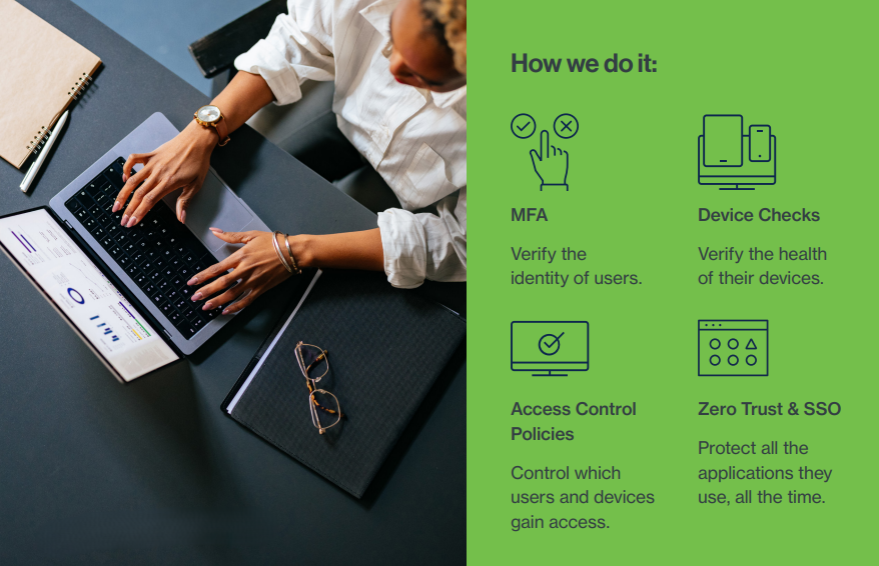
Duo Access Management is a security solution that gives you layers of authentication protection and access control by confirming that you're really who you say you are before access is granted to your accounts and corporate data. With Duo, even if someone knows your password, unless they have your trusted device – mobile phone, tablet, token, or Apple Watch – Duo can stop them in their tracks.
Rapid deployments, faster end-user adoption, and the ability to respond quickly to changing threats.
Stay flexible with a hybrid work environment without slowing down users.
Focus on growing your business, rather than restricting it.
Meet and Exceed Security Compliance Initiatives:
Duo helps customers meet compliance standards including Cyber Liability Insurance requirements and the new FTC Safeguards rules.
Reduce MFA Fatigue:
With Duo Single-Sign On, Passwordless, and Remembered Devices, users won't need to constantly re-authenticate.
Security by Group:
Flexible policy design at the application, group, or global level ensures only authorized users gain access.
Secure OS Logon:
Ensure endpoint security by protecting Windows or macOS login, including offline access and server access.
There are a variety of methods users can leverage at admin discretion: Duo Push, Passcode, SMS, Phone Callback, WebAuthn, and Hardware Tokens.
Increases security and reduces risk of push harassment and attacks by adding a verification code into the Duo Push workflow.
Detect authentication risk, prior to granting access, and automatically step-up authentication as needed.
Duo SSO is a cloud-hosted solution which acts as an identity provider that secures access to cloud applications with existing directory credentials.
Remove the need for end-user password input while increasing security at the time of authentication into cloud and SAML-based applications.
Build out a Zero Trust strategy by identifying risky devices, enforcing contextual access policy, and report on device health without an agent.
Microsoft Enterprise solutions provide comprehensive business intelligence, productivity, and security capabilities designed for organizations of all sizes. Our partnership combines Microsoft's industry-leading platform with StackOps' specialized implementation expertise to deliver tailored solutions that maximize ROI, enhance collaboration, and strengthen security posture across your organization.

Microsoft Certified professionals who understand your unique business needs and implement solutions that scale.
Seamlessly connected solutions across Microsoft 365, Azure, and Dynamics platforms.
Built-in advanced security with threat protection and compliance management.
Ongoing optimization and support to ensure your solutions evolve with your business.
Drive Digital Transformation:
Organizations worldwide use Microsoft solutions to modernize operations, improve
employee collaboration, and unlock data-driven insights.
Hybrid Work Enablement:
Microsoft Teams, SharePoint, and cloud infrastructure support seamless collaboration
whether employees are on-site or remote.
Business Intelligence & Analytics:
Power BI and analytics services transform raw data into actionable insights for
strategic decision-making.
Cloud-First Strategy:
Azure cloud services provide scalability, reliability, and cost-effectiveness for
modern application deployment and management.
Integrated productivity suite with Word, Excel, PowerPoint, Teams, Exchange, and SharePoint for modern workplace collaboration.
Scalable cloud platform supporting virtual machines, databases, AI services, and enterprise application hosting.
Business intelligence and data visualization tools that transform data into compelling insights and dashboards.
Enterprise resource planning and customer relationship management with AI-driven insights for business optimization.
Comprehensive threat protection across endpoints, identities, cloud, and applications with advanced threat analytics.
AI-powered productivity enhancements integrated across Microsoft 365 apps and enterprise applications for intelligent automation.
Managing your organization's IT infrastructure shouldn't be a guessing game. StackCTRL is our centralized, state-of-the-art client portal designed to give you total visibility and absolute control over your entire IT ecosystem. From real-time threat detection to proactive device management and license tracking, StackCTRL transforms complex security data into clear, actionable insights.

Security isn't just a feature; it's the foundation.
Consolidate your entire IT landscape into a single, intuitive interface.
Stop threats before they start with real-time analytics.
Keep track of your investments and compliance effortlessly.
Cisco Duo License Monitoring:
Never lose track of your security investments. Seamlessly monitor your purchased Cisco Duo licenses, track active usage, view your current edition tier, and see exactly how many seats you have remaining—all synced directly to your dashboard.
Real-Time Threat Response (SOC):
Act instantly with a live activity feed. Alerts are automatically categorized by severity (Critical, High, Medium), so your IT team knows exactly what to prioritize and how to fix it.
Governance & Billing Hub:
Maintain full compliance with built-in SLA monitoring and governance evidence tracking. Plus, keep your finances organized with direct access to your billing statements, invoices, and payment statuses.
Resilient Backup & Recovery:
Data loss is not an option. Track storage usage and backup health across your entire cloud ecosystem to forecast future needs before you run out of space.
Instantly track active users, internal vs. external accounts, and identify stale profiles. Keep a close watch on your most powerful accounts by automatically flagging excessive admin privileges and users operating without MFA.
Instantly see which company devices are fully encrypted, actively managed, and compliant with your corporate policies. Audit connected applications to flag those with excessive permissions or high-risk access levels.
Automatically identify and categorize incoming threats like sophisticated Phishing attempts, Malware, and Spam. Discover exactly which users in your organization are being targeted to provide timely security intervention.
Direct integration allows you to view your Cisco Duo license counts, monitor active usage, and verify your subscription tiers without leaving the portal.
Contact us today to discuss your project requirements